Azure Identity Services: Imagine Azure as a bustling city, with various buildings and facilities representing its various resources and applications. Azure Identity Services are like the city’s identification system, ensuring that only recognized and authorized individuals can access specific locations and services within the city. This system includes various components such as Authentication, Authorization, Azure Active Directory (AD), Multi-Factor Authentication (MFA), Single Sign-On (SSO), and Conditional Access.
Authentication: This is like the city gate where guards verify who you are before you enter. It’s the process of confirming your identity. When a resident arrives at the gate, they must show their ID card (like a username) and sometimes provide a password or another form of identification. In Azure, this is where users prove who they are, typically through a login process.
Authorization: Once inside the city, Authorization comes into play. Think of it as the various signs and barriers throughout the city that determine where residents can go and what they can do. After you’re authenticated and inside the city, authorization is the process that decides which buildings you can enter and what services you can use. In Azure, this means determining what resources a user can access and what they can do with them.
Learn and SkillPipe content:
Azure Active Directory (AD): Think of Azure AD as the city’s population registry, where every resident (user) and their roles are listed. It’s a comprehensive identity and access management cloud solution, providing a robust set of capabilities to manage users and groups. It helps secure access to internal and external resources, much like how a city registry would determine which residents can access certain municipal services.
Learn and SkillPipe content:
Multi-Factor Authentication (MFA): MFA in Azure is akin to a security checkpoint in our city analogy, where residents must provide multiple proofs of identity before being granted access. It adds a critical second layer of security to user sign-ins and transactions, like a security officer asking for both an ID card and a passcode before allowing entry into a secure facility.
Single Sign-On (SSO): SSO simplifies the process of accessing multiple services in the city. Imagine if residents could visit various facilities—like the library, gym, or community center—without needing to prove their identity each time. SSO allows users to log in once and access a range of applications and services without having to sign in again and again.
Conditional Access: This is the city’s smart access system, where the conditions of entry into specific areas can vary based on certain factors. It uses policies that assess the context of a user’s attempt to access resources, adjusting the required level of authentication accordingly. For instance, entry into a high-security facility might depend not just on who is requesting access, but also on when and from where they are making the request.
Let’s say you’re managing a team in this Azure city. You have a group of employees who need to access the finance department’s building (a specific resource) regularly. With Azure AD, you register each team member, granting them a unique identity within the city. To enhance security, you implement MFA, requiring them to provide a password and a fingerprint scan at the building’s entrance. For ease of access to various buildings (applications) across the city, you enable SSO, so they don’t have to repeatedly verify their identity. And with Conditional Access, you set policies that restrict access to the finance building outside of office hours, or when attempts are made from untrusted locations. This way, you ensure secure, efficient, and controlled access to your Azure resources.
Now we’re going to explore some fundamental concepts in Azure Governance Methodologies, designed to help you understand and manage your Azure resources, even if you’re just starting out. We’ll discuss Role-Based Access Control (RBAC), Resource locks, Tags, Azure Policy, Azure Blueprints, and the Cloud Adoption Framework for Azure.
- Role-Based Access Control (RBAC): Imagine Azure as a huge office building with different rooms and resources. RBAC is like the keys and access cards that determine who can enter which rooms and what they can do once they’re inside. In Azure, RBAC helps you control who has access to your resources and what actions they can perform.For example, let’s say you have a team of developers and you want to give them access to create virtual machines but not delete them. You can create a custom role in RBAC to grant them those specific permissions without giving them full administrative access.
Learn and SkillPipe content:
- Resource Locks: Resource locks are like those “Do Not Disturb” signs you hang on your hotel room door. They prevent accidental deletion or modification of critical resources. So, you can use them to protect important resources from being altered or deleted, even by someone with the right permissions.For instance, if you have a production database that should never be deleted accidentally, you can apply a resource lock to ensure it stays safe and untouched.
Learn and SkillPipe content:
- Tags: Tags are like sticky notes you can attach to your Azure resources. They help you organize and categorize your resources in a way that makes sense to your organization. You can use tags to track costs, manage resources by department, or identify the owner of a resource.Let’s say you have a bunch of virtual machines for different projects. You can tag each VM with the project name, making it easy to see which resources belong to which project and manage costs accordingly.
Learn and SkillPipe content:
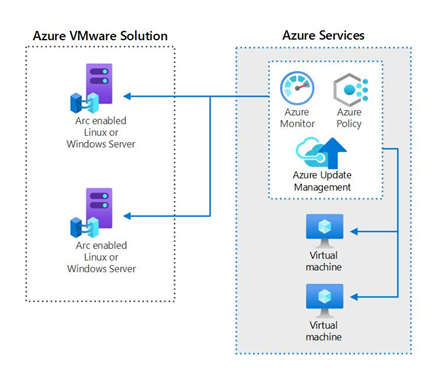
- Azure Policy: Azure Policy is like a rulebook for your Azure environment. It lets you define and enforce rules and standards for your resources. You can ensure that your resources comply with your organization’s policies and best practices.For instance, you can create a policy that ensures all virtual machines have encryption enabled or that only approved virtual machine images are used.
Learn and SkillPipe content:
- Azure Blueprints: Azure Blueprints are like templates for your Azure environment. They allow you to define a repeatable set of resources, policies, and roles that can be applied to new subscriptions. It’s a way to ensure that every new project or department in your organization starts with the same foundation.Imagine you have a standard setup for compliance that includes specific resources, policies, and roles. With Azure Blueprints, you can easily replicate that setup for each new project, saving time and ensuring consistency.
Learn and SkillPipe content:
- Cloud Adoption Framework for Azure: The Cloud Adoption Framework is like a roadmap for your cloud journey. It provides guidance, best practices, and resources to help you plan and execute your Azure adoption.Suppose you’re a company looking to migrate your on-premises applications to Azure. The Cloud Adoption Framework can help you define your strategy, assess your current environment, and plan the migration step by step.
Learn and SkillPipe content:
Privacy, Compliance, and Data Protection
Think of these as the three pillars that hold up the Microsoft ecosystem. Security, Privacy, and Compliance are at the heart of everything Microsoft does.
- Security ensures that your data and resources are safeguarded from threats. Microsoft employs robust measures to protect your information from cyberattacks.
- Privacy focuses on respecting your data and giving you control over it. Microsoft is committed to transparency regarding data collection and use.
- Compliance is about adhering to legal and regulatory requirements. Microsoft ensures that its services comply with various global standards and regulations, helping you meet your own compliance needs like GDPR, HIPAA, etc.
Learn and SkillPipe content:
Microsoft privacy statement
Privacy Statement explains what data Microsoft collects and how they use it. For example, when you use Microsoft 365, they collect data to provide you with personalized experiences.
Learn and SkillPipe content:
Online Services Terms (OST) are like the rules of engagement when you use Microsoft’s online services. They cover everything from usage rights to compliance requirements.
Data Protection Amendment (DPA) is an additional contract that specifies how Microsoft handles your data in compliance with data protection laws.
Learn and SkillPipe content:
Trust Center is like the control room where Microsoft manages and communicates its commitment to security, privacy, and compliance. It provides resources, reports, and certifications to help you understand and trust Microsoft’s practices.
Learn and SkillPipe content:
Azure Compliance Documentation: This is your go-to resource for understanding how Azure services comply with various industry standards and regulations.
Let’s say you work in healthcare and need to ensure that your data in Azure complies with HIPAA regulations. Azure compliance documentation will guide you through Azure’s HIPAA compliance features and practices.
Learn and SkillPipe content:
Azure Sovereign Regions (Azure Government and Azure China)
Azure Sovereign Regions are like dedicated, specialized environments within Azure. Azure Government is designed for U.S. government agencies, while Azure China serves customers in China.
If you’re a government agency dealing with sensitive information, you’d want to use Azure Government to ensure that your data stays within the government’s jurisdiction and adheres to specific compliance requirements.
Learn and SkillPipe content: